KYC Interview Question and Answers
Last Updated on Mar 27, 2026, 2k Views

KYC Interview Question and Answers
1. What is KYC?
Answer:
KYC (Know Your Customer) is the process of verifying the identity of customers to prevent fraud, money laundering, and illegal activities. It ensures that financial institutions know who their customers are.
2. Why is KYC important?
Answer:
KYC is important because it:
Prevents money laundering and fraud
Helps banks comply with regulations
Builds trust and transparency
Protects the financial system
3. What documents are required for KYC?
Answer:
Common documents include:
Identity Proof (Aadhaar, PAN, Passport)
Address Proof (Utility bill, Driving license)
Photograph
PAN card (mandatory for financial transactions in India)
4. What is the difference between KYC and AML?
Answer:
KYC: Identifies and verifies customers
AML (Anti-Money Laundering): Detects and prevents illegal financial activities
👉 KYC is a part of AML.
5. What is Customer Due Diligence (CDD)?
Answer:
CDD is the process of collecting and verifying customer information to assess risk before onboarding.
6. What are the types of KYC?
Answer:
Simplified KYC – Low-risk customers
Full KYC – Complete verification
e-KYC – Digital verification (Aadhaar-based)
Video KYC – Remote verification through video call
7. What is e-KYC?
Answer:
e-KYC is an electronic process of verifying identity using Aadhaar and OTP or biometric authentication.
8. What is Video KYC?
Answer:
Video KYC allows verification through a live video call where the customer shows documents and answers questions.
9. What is PEP?
Answer:
PEP (Politically Exposed Person) is someone who holds a prominent public position (e.g., ministers, government officials) and is considered higher risk.
10. What is a Suspicious Transaction?
Answer:
A transaction that appears unusual or inconsistent with a customer’s profile, such as large cash deposits or frequent international transfers.
11. What is KYC periodic update?
Answer:
It is the process of updating customer information regularly to ensure records remain accurate and compliant.
12. What is FATF?
Answer:
The Financial Action Task Force is an international organization that sets standards to combat money laundering and terrorist financing.
13. What is Risk-Based Approach in KYC?
Answer:
It means applying different levels of checks depending on customer risk:
Low risk → basic checks
High risk → enhanced due diligence
14. What is Enhanced Due Diligence (EDD)?
Answer:
EDD is a deeper investigation for high-risk customers like PEPs or foreign clients.
15. What is KYC onboarding?
Answer:
It is the process of verifying a customer before opening an account or starting a business relationship.
16. What is Customer Due Diligence (CDD)?
Answer:
CDD is the process of verifying a customer’s identity and assessing their risk profile before onboarding. It includes:
Identity verification (KYC documents)
Understanding nature of business
Risk classification (Low/Medium/High)
17. What is Enhanced Due Diligence (EDD)?
Answer:
EDD is applied to high-risk customers such as:
Politically Exposed Persons (PEPs)
High-risk countries
Complex ownership structures
It involves:
Source of funds/wealth verification
Senior management approval
Ongoing monitoring
18. What is the difference between KYC and AML?
Answer:
KYC: Identifying and verifying customers
AML (Anti-Money Laundering): Monitoring and preventing illegal financial activities
👉 KYC is a part of AML framework.
19. What is a Politically Exposed Person (PEP)?
Answer:
A PEP is an individual who holds a prominent public position (e.g., ministers, MPs) and poses higher corruption risk.
Types:
Domestic PEP
Foreign PEP
Close associates/family members
20. What is Ultimate Beneficial Owner (UBO)?
Answer:
UBO is the natural person who ultimately owns or controls a legal entity (usually holding ≥25% ownership or control).
21. What is Risk-Based Approach (RBA)?
Answer:
RBA means applying controls based on risk level:
Low risk → Simplified checks
Medium risk → Standard CDD
High risk → Enhanced Due Diligence
22. What are sanctions and watchlists?
Answer:
Sanctions are restrictions imposed by authorities on individuals/entities.
Examples:
Office of Foreign Assets Control (OFAC)
United Nations Security Council
Watchlists are screened during onboarding and transactions.
23. What is ongoing monitoring in KYC?
Answer:
Continuous review of customer transactions and profile to detect suspicious activity:
Transaction monitoring
Periodic KYC refresh
Trigger-based reviews
24. What are red flags in KYC?
Answer:
Examples include:
Mismatch in customer information
Unusual transaction patterns
Use of shell companies
Frequent large cash transactions
25. What is periodic review / KYC refresh?
Answer:
Updating customer information at regular intervals:
High risk → 1 year
Medium risk → 2–3 years
Low risk → 3–5 years
26. What is FATF and its role?
Answer:
Financial Action Task Force is an international body that sets AML/CFT standards and guidelines followed globally.
27. What is the difference between individual and non-individual KYC?
Answer:
Individual KYC: ID proof, address proof
Non-individual KYC (corporate):
Certificate of incorporation
Board resolution
UBO identification
28. What is source of funds vs source of wealth?
Answer:
Source of Funds (SOF): Origin of a specific transaction (e.g., salary, sale)
Source of Wealth (SOW): Overall wealth origin (e.g., business, inheritance)
29. What is a shell company?
Answer:
A company with no real operations, often used to hide ownership or launder money.
30. What is name screening?
Answer:
Process of checking customer names against:
Sanctions lists
PEP lists
Adverse media
31. What are false positives in screening?
Answer:
When a system flags a match incorrectly due to similar names (e.g., common names).
32. What is STR/SAR?
Answer:
STR: Suspicious Transaction Report
SAR: Suspicious Activity Report
Filed with regulators when suspicious activity is detected.
33. What is PMLA in India?
Answer:
Prevention of Money Laundering Act is the primary law to prevent money laundering in India.
34. What is Customer Identification Program (CIP)?
Answer:
CIP ensures collection and verification of:
Name
Date of birth
Address
Identification number
35. What is KYC remediation?
Answer:
Process of updating incomplete or outdated KYC records to meet compliance standards.
36. Risk-Based Approach (RBA)
What is a Risk-Based Approach in KYC and why is it important?
How do you categorize customers into low, medium, and high risk?
What factors influence customer risk rating?
How often should KYC be reviewed for different risk categories?
How do you handle a high-risk customer onboarding?
37. Customer Due Diligence (CDD) & Enhanced Due Diligence (EDD)
Explain the difference between CDD, EDD, and Simplified Due Diligence (SDD).
When is EDD mandatory?
What additional checks are performed during EDD?
How do you verify the authenticity of documents submitted by customers?
What is ongoing due diligence?
38. Ultimate Beneficial Ownership (UBO)
What is UBO and why is it critical in KYC?
How do you identify UBO in complex corporate structures?
What threshold is used to identify UBO (e.g., 25%)?
How do you handle cases where UBO cannot be identified?
What documents are required to verify UBO?
39. Regulatory Framework & Compliance
What is the role of Financial Action Task Force in KYC/AML?
Explain key provisions of Prevention of Money Laundering Act.
What are the guidelines issued by Reserve Bank of India for KYC?
What is Financial Intelligence Unit – India and its role?
What are sanctions lists and how do you screen them?
40. Politically Exposed Persons (PEPs)
What is a PEP? Types of PEPs?
Why are PEPs considered high-risk?
What additional due diligence is required for PEPs?
How do you monitor PEP accounts?
What is adverse media screening?
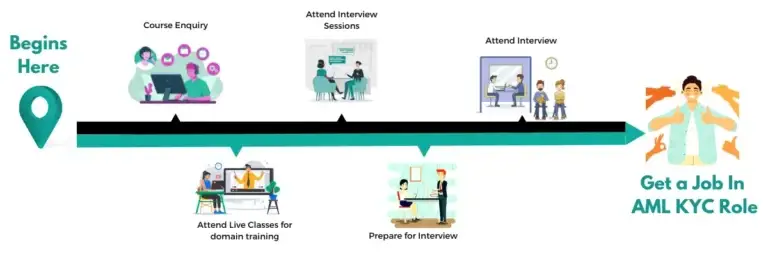
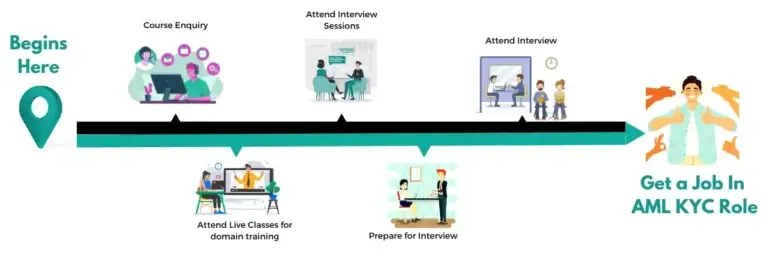
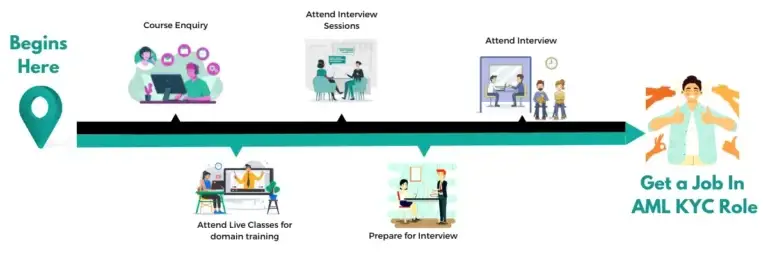
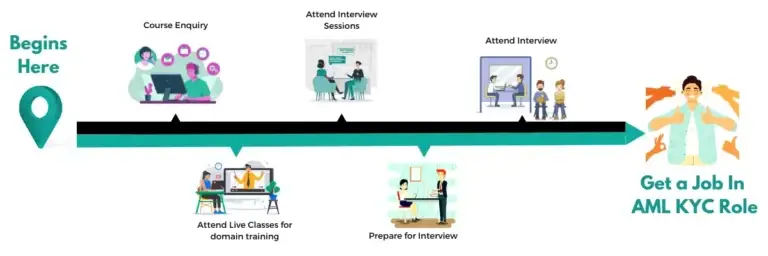
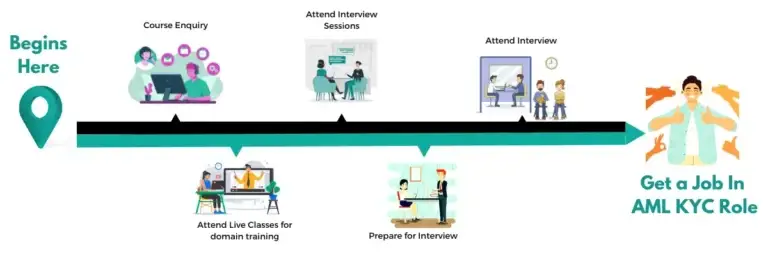
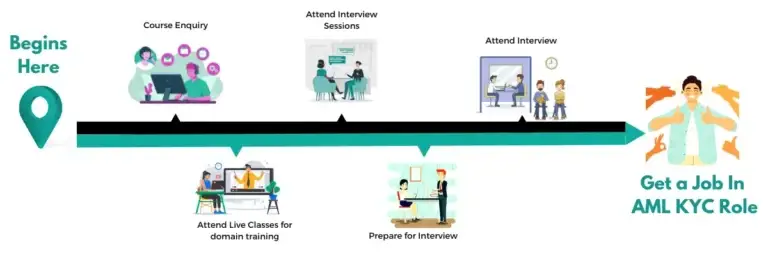
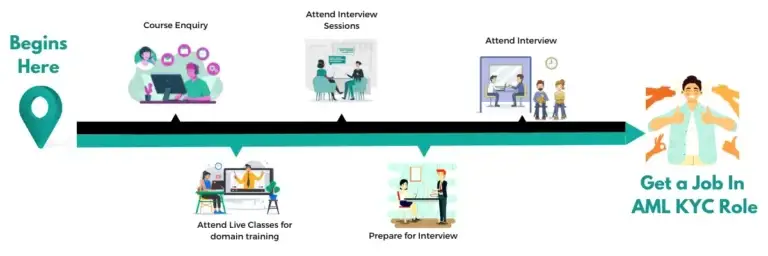
Career Advice!
Feel Free to Contact Us or WhatsApp Us for Career Counseling!
- +91 9066508122
Data Science Interview Questions
Data Science Interview Questions Data Science Interview Questions 1. What...
Read MoreTop 30 DevOps Interview Questions & Answers (2022 Update)
Top 30 DevOps Interview Questions & Answers (2022 Update) Top...
Read MoreAnti Money Laundering Interview Questions
Anti Money Laundering Interview Questions Anti Money Laundering Interview Questions...
Read More